AWS Control Tower and Foundational Infrastructure Setup
A fast-growing EdTech SaaS company
Client
A fast-growing EdTech SaaS company providing a fundraising platform for colleges, universities, and K–12 schools. As a cloud-native organization planning a full migration from a third-party PaaS to AWS, they required a robust, enterprise-grade cloud foundation before migration could begin.
Challenge
The client lacked the foundational AWS infrastructure required to proceed with migration safely:
- No AWS Organizations structure or multi-account strategy
- No AWS Control Tower Landing Zone, guardrails, or account baselines
- Google Workspaces not integrated with AWS Identity Center—no centralized SSO
- No Transit Gateway or dedicated Networking account for cross-account connectivity
- GuardDuty and Security Hub not configured—no threat detection or security monitoring
- No Terraform IaC—no repeatable, auditable, or version-controlled provisioning
Key Results
- Delivered a complete 7-account AWS multi-account foundation in 2 weeks, accelerating migration readiness by 80%
- Reduced manual provisioning effort by 60% through a fully modular Terraform IaC framework with S3 remote state
- Achieved centralized identity federation across all accounts via Google Workspaces SAML and AWS Identity Center
- Reduced mean time to detect (MTTD) threats by 40% through GuardDuty and Security Hub across all accounts and regions
Solution
Delivered over a two-week engagement in five structured phases:
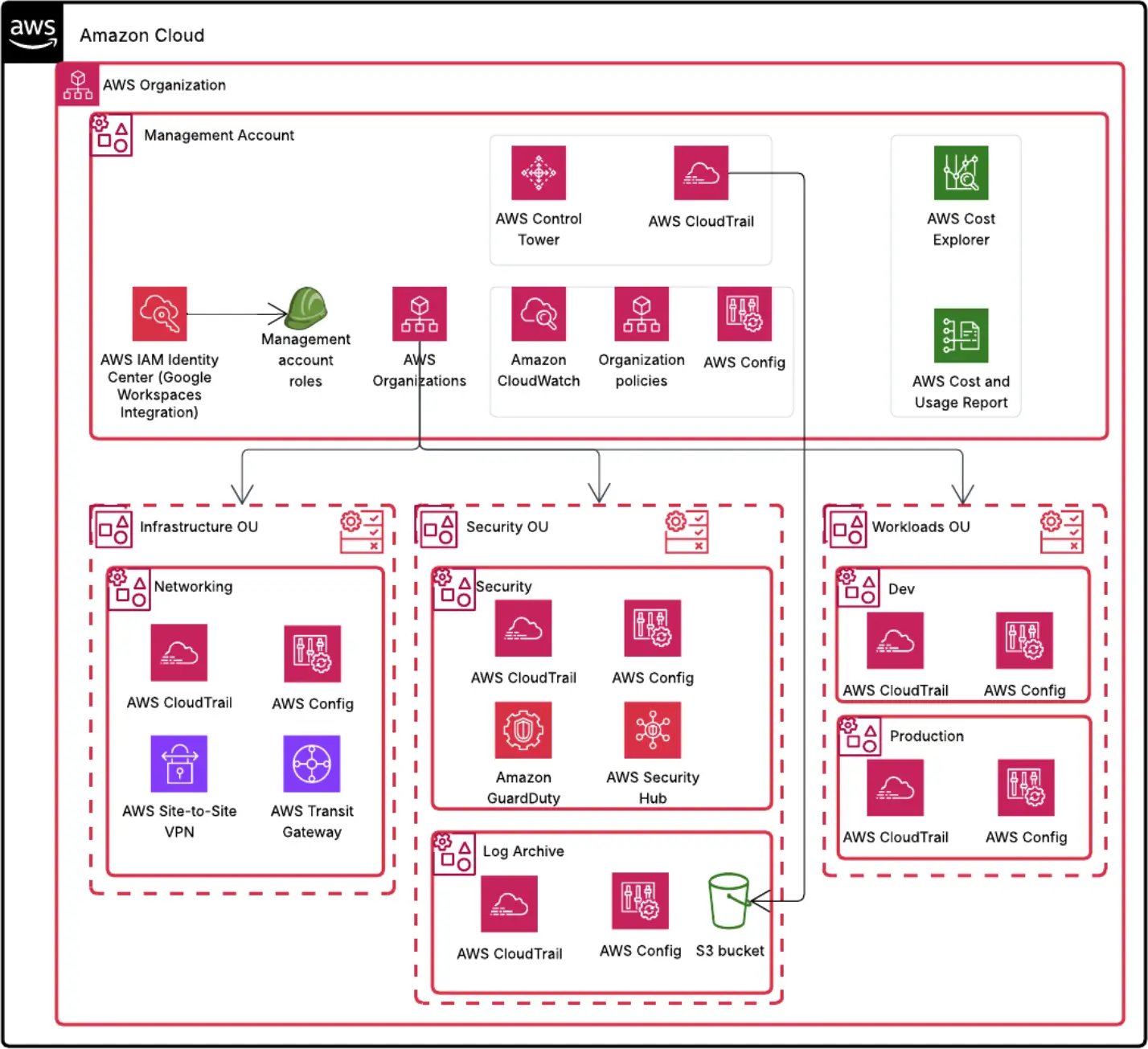
- Analysis & Foundation: Configured AWS Organizations with a 7-account hierarchy (Management, Networking, Production, Development, Audit, Log Archive). Deployed Control Tower Landing Zone with guardrails, account baselines, and Account Factory. Set up Terraform with S3 remote state.
- Identity & Security: Integrated Google Workspaces with AWS Identity Center via SAML for cross-account SSO. Configured least-privilege permission sets, CloudTrail, Config, GuardDuty (all accounts/regions), and Security Hub with multi-account aggregation.
- Network Infrastructure: Established a dedicated Networking account with a VPC and Transit Gateway, segmented route tables, and cross-account routing controls.
- Account Integration: Deployed Production and Development VPCs with multi-AZ subnets, attached to the Transit Gateway with environment-specific route tables, security groups, and NACLs. Validated end-to-end connectivity and identity integration.
- Documentation & Handover: Delivered architecture diagrams, multi-account and security strategy docs, and Terraform module documentation. Conducted a formal knowledge transfer session.
Technologies Used
- AWS Control Tower & AWS Organizations
- AWS Identity Center (SSO) & Google Workspaces (SAML)
- AWS Transit Gateway
- AWS GuardDuty & Security Hub
- AWS CloudTrail & AWS Config
- Terraform (IaC)
Summary
A fast-growing ed-fundraising SaaS needed a secure, scalable AWS cloud foundation. In two weeks, we built a seven-account AWS Organizations setup with Control Tower guardrails, Google SAML via AWS Identity Center, centralized Transit Gateway networking, GuardDuty and Security Hub monitoring, and a modular Terraform IaC framework—readying them for a confident cloud migration.
#arocom #artificialintelligence #machinelearning #datascience


